4 OKR examples for Vulnerability
What are Vulnerability OKRs?
The OKR acronym stands for Objectives and Key Results. It's a goal-setting framework that was introduced at Intel by Andy Grove in the 70s, and it became popular after John Doerr introduced it to Google in the 90s. OKRs helps teams has a shared language to set ambitious goals and track progress towards them.
OKRs are quickly gaining popularity as a goal-setting framework. But, it's not always easy to know how to write your goals, especially if it's your first time using OKRs.
We've tailored a list of OKRs examples for Vulnerability to help you. You can look at any of the templates below to get some inspiration for your own goals.
If you want to learn more about the framework, you can read more about the OKR meaning online.
Best practices for managing your Vulnerability OKRs
Generally speaking, your objectives should be ambitious yet achievable, and your key results should be measurable and time-bound (using the SMART framework can be helpful). It is also recommended to list strategic initiatives under your key results, as it'll help you avoid the common mistake of listing projects in your KRs.
Here are a couple of best practices extracted from our OKR implementation guide 👇
Tip #1: Limit the number of key results
Having too many OKRs is the #1 mistake that teams make when adopting the framework. The problem with tracking too many competing goals is that it will be hard for your team to know what really matters.
We recommend having 3-4 objectives, and 3-4 key results per objective. A platform like Tability can run audits on your data to help you identify the plans that have too many goals.
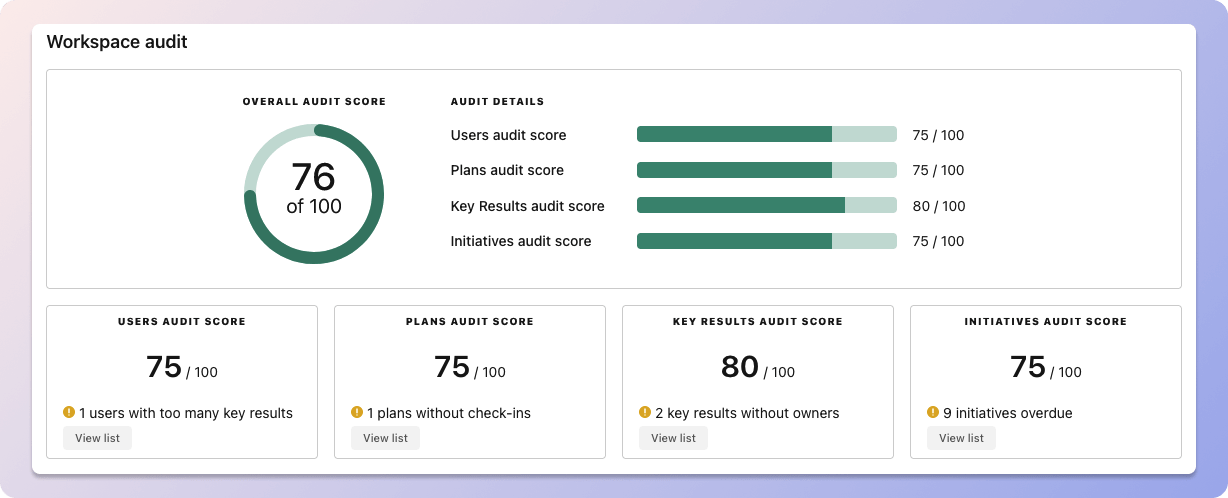 Tability's audit dashboard will highlight opportunities to improve OKRs
Tability's audit dashboard will highlight opportunities to improve OKRsTip #2: Commit to the weekly check-ins
Setting good goals can be challenging, but without regular check-ins, your team will struggle to make progress. We recommend that you track your OKRs weekly to get the full benefits from the framework.
Being able to see trends for your key results will also keep yourself honest.
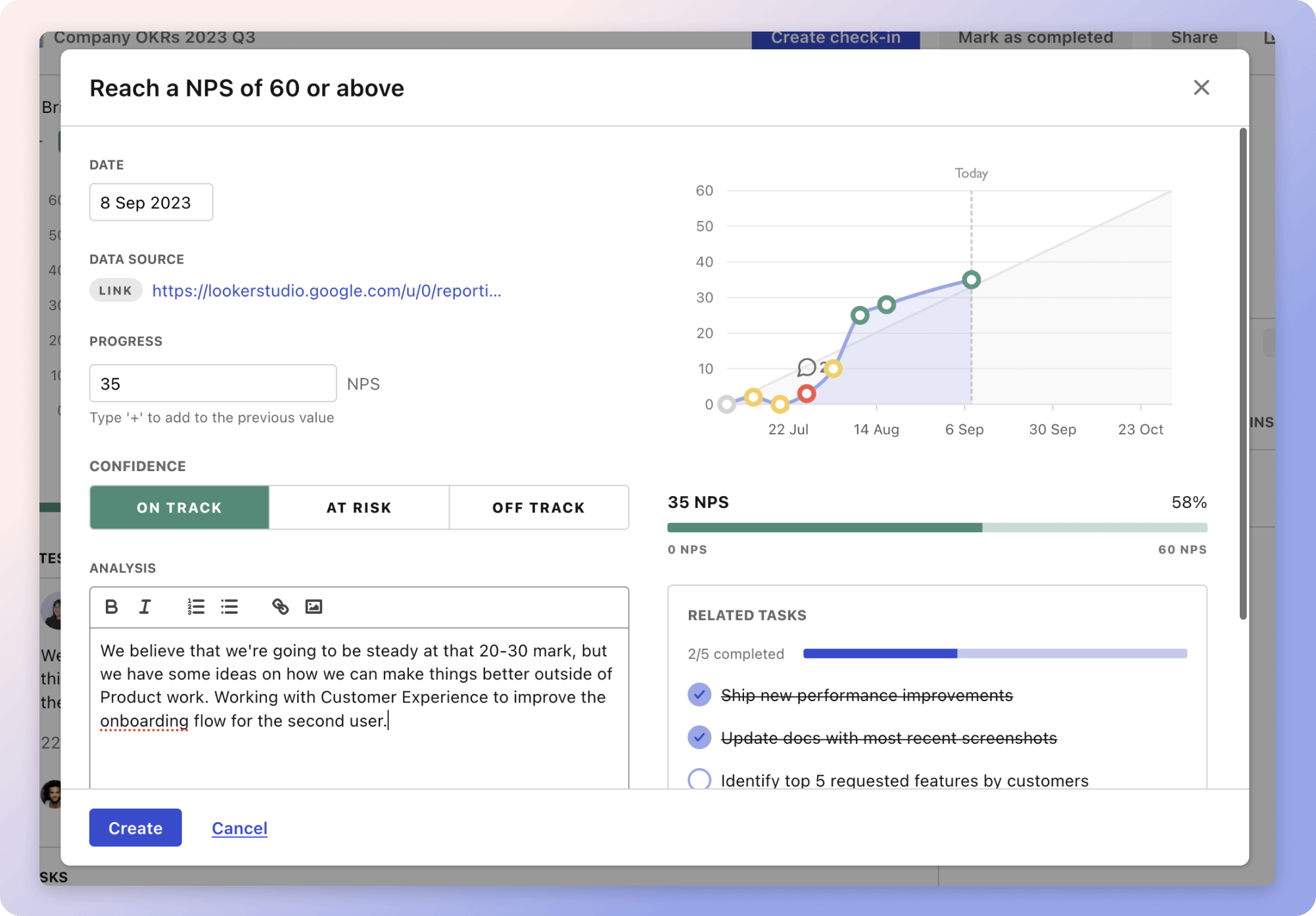 Tability's check-ins will save you hours and increase transparency
Tability's check-ins will save you hours and increase transparencyTip #3: No more than 2 yellow statuses in a row
Yes, this is another tip for goal-tracking instead of goal-setting (but you'll get plenty of OKR examples below). But, once you have your goals defined, it will be your ability to keep the right sense of urgency that will make the difference.
As a rule of thumb, it's best to avoid having more than 2 yellow/at risk statuses in a row.
Make a call on the 3rd update. You should be either back on track, or off track. This sounds harsh but it's the best way to signal risks early enough to fix things.
Building your own Vulnerability OKRs with AI
While we have some examples below, it's likely that you'll have specific scenarios that aren't covered here. There are 2 options available to you.
- Use our free OKRs generator
- Use Tability, a complete platform to set and track OKRs and initiatives
- including a GPT-4 powered goal generator
Best way to track your Vulnerability OKRs
OKRs without regular progress updates are just KPIs. You'll need to update progress on your OKRs every week to get the full benefits from the framework. Reviewing progress periodically has several advantages:
- It brings the goals back to the top of the mind
- It will highlight poorly set OKRs
- It will surface execution risks
- It improves transparency and accountability
Most teams should start with a spreadsheet if they're using OKRs for the first time. Then, once you get comfortable you can graduate to a proper OKRs-tracking tool.
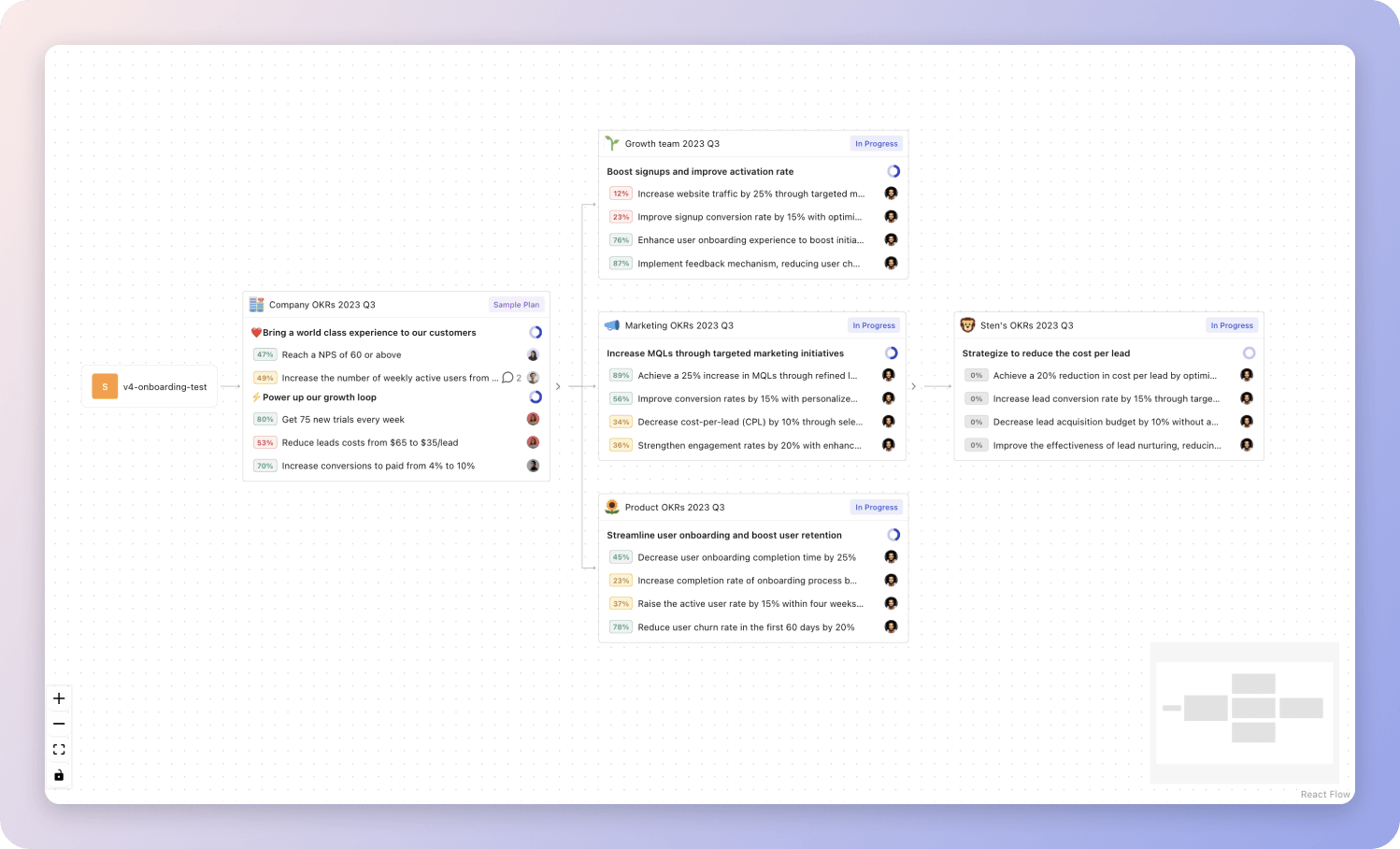 Tability's Strategy Map makes it easy to see all your org's OKRs
Tability's Strategy Map makes it easy to see all your org's OKRsIf you're not yet set on a tool, you can check out the 5 best OKR tracking templates guide to find the best way to monitor progress during the quarter.
Vulnerability OKRs templates
We've covered most of the things that you need to know about setting good OKRs and tracking them effectively. It's now time to give you a series of templates that you can use for inspiration!
We've added many examples of Vulnerability Objectives and Key Results, but we did not stop there. Understanding the difference between OKRs and projects is important, so we also added examples of strategic initiatives that relate to the OKRs.
Hope you'll find this helpful!
OKRs to implement effective vulnerability management processes
Strengthen our vulnerability management procedures
Reduce high-priority vulnerabilities by 30% through consistent scanning and patching
Train all employees on vulnerability management best practices and create an awareness program
Implement a continuous vulnerability scanning process for all systems and applications
Develop and implement a comprehensive vulnerability management policy based on industry standards
OKRs to enhance Product's Cybersecurity
Enhance Product's Cybersecurity
Implement two additional layers of authentication for user access to sensitive data
Reduce the average response time for resolving cybersecurity incidents by 20%
Implement real-time threat monitoring and detection systems to identify and respond to incidents promptly
Conduct regular cybersecurity training and awareness programs to improve incident response capabilities
Enhance collaboration and communication between cybersecurity teams to streamline incident resolution processes
Develop and implement standardized incident response procedures for efficient and effective resolution
Conduct a comprehensive vulnerability assessment and address identified issues within two weeks
Increase cybersecurity training completion rate to 90% for all employees
Conduct regular assessments and evaluations to identify and address any barriers to training completion
Implement a regular reminder system to notify employees about pending training and deadlines
Develop engaging online cybersecurity training modules with interactive exercises and gamification elements
Provide incentives and rewards for employees who complete cybersecurity training on time
OKRs to enhance data privacy and cybersecurity measures to safeguard sensitive information
Enhance data privacy and cybersecurity measures to safeguard sensitive information
Implement a comprehensive data encryption system across all relevant platforms
Assess current data encryption measures and identify gaps for improvement
Develop and implement a standardized data encryption protocol for all platforms
Conduct regular audits to ensure consistent adherence to the data encryption system
Train employees on proper data encryption practices and its importance in data security
Conduct regular vulnerability assessments and address identified risks within set timeframes
Quickly prioritize and address identified risks based on severity levels
Schedule regular vulnerability assessments according to established timelines
Establish set timeframes for risk mitigation and ensure timely execution
Develop a clear process for tracking and documenting vulnerability assessment findings
Increase employee awareness and participation in cybersecurity training programs by 25%
Recognize and reward employees who actively participate in cybersecurity training
Create engaging and interactive modules for cybersecurity training programs
Organize lunch and learn sessions to promote employee awareness about cybersecurity threats
Send regular email reminders about upcoming cybersecurity training sessions
Achieve a 10% improvement in overall incident response time, ensuring timely mitigation of potential breaches
Streamline incident response processes and eliminate any unnecessary steps for faster response times
Regularly evaluate and improve incident response plans to enhance efficiency and effectiveness
Provide comprehensive training to all personnel involved in incident response procedures
Implement automation tools to expedite the identification and containment of potential breaches
OKRs to conduct regular penetration testing and code reviews
Improve security through regular penetration testing and code reviews
Ensure all critical vulnerabilities found in penetration testing are remediated within 2 weeks
Conduct code reviews for all new features and major changes before deployment
Implement at least 80% of code review recommendations within the next release cycle
Increase the frequency of penetration testing from once a quarter to twice a month
More Vulnerability OKR templates
We have more templates to help you draft your team goals and OKRs.
OKRs to foster customer-centric culture through UX insights
OKRs to enhance finance department's risk management initiatives
OKRs to foster inclusivity in the workplace
OKRs to boost the volume of organic traffic to our website
OKRs to optimize CPA by reducing it by 15%
OKRs to expand legal and regulatory resources network
OKRs resources
Here are a list of resources to help you adopt the Objectives and Key Results framework.
- To learn: Complete 2024 OKR cheat sheet
- Blog posts: ODT Blog
- Success metrics: KPIs examples